EVO version 7 introduces SSL LDAP user integration, allowing for faster and more secure SMB access for LDAP users.
The following example shows how to configure a v7 EVO to add external users from a JumpCloud LDAP instance, and requires:
- Admin access to a v7 EVO with external network access (working gateway and DNS provider)
- Access to the JumpCloud Admin Portal with an LDAP Binding User and Samba Service Account
Use the Ping test on EVO's Network page to confirm network access.
If using JumpCloud, a certificate is included in EVO, and no import is needed.
If using an alternative samba schema LDAP server, a trusted G2 root CA will need to be provided (this example uses a GoDaddy Class 2 Root Authority certificate).
import your certificate file at System > Advanced > Certificate authority.
Configuring the LDAP server will require some EVO-specific information. Make a note of the following from EVO's web interface:
- Host name, shown at the Network > Network service advertising card
If the host name has changed, make sure to reboot before proceeding.
- Samba SID, displayed at Users > External Users > LDAP. Select External users from the dropdown menu on the left to expose the AD/LDAP button on the right.
Click the AD/LDAP button and then select the LDAP tab to expose the menu and copy the SID.
Be sure to copy the entire string.
If using JumpCloud, toggle "Enable support for Jumpcloud groups"
At the JumpCloud Admin Portal:
Make sure the LDAP instance is configured for Samba Authentication using a Samba Service Account.
Enter EVO's host name in the Workgroup field at the LDAP > JumpCloud LDAP > Details page.
Enter EVO's Samba SID in the SID field.
Check that Samba Authentication is enabled for the group of users that should be visible to EVO at the User Groups page.
A Samba Service Account and LDAP Binding user are required for authentication to the directory.
Now configuring EVO will require some LDAP-specific information. The values in the ORG DN field and the Samba Service Account DN field will be used to complete the setup.
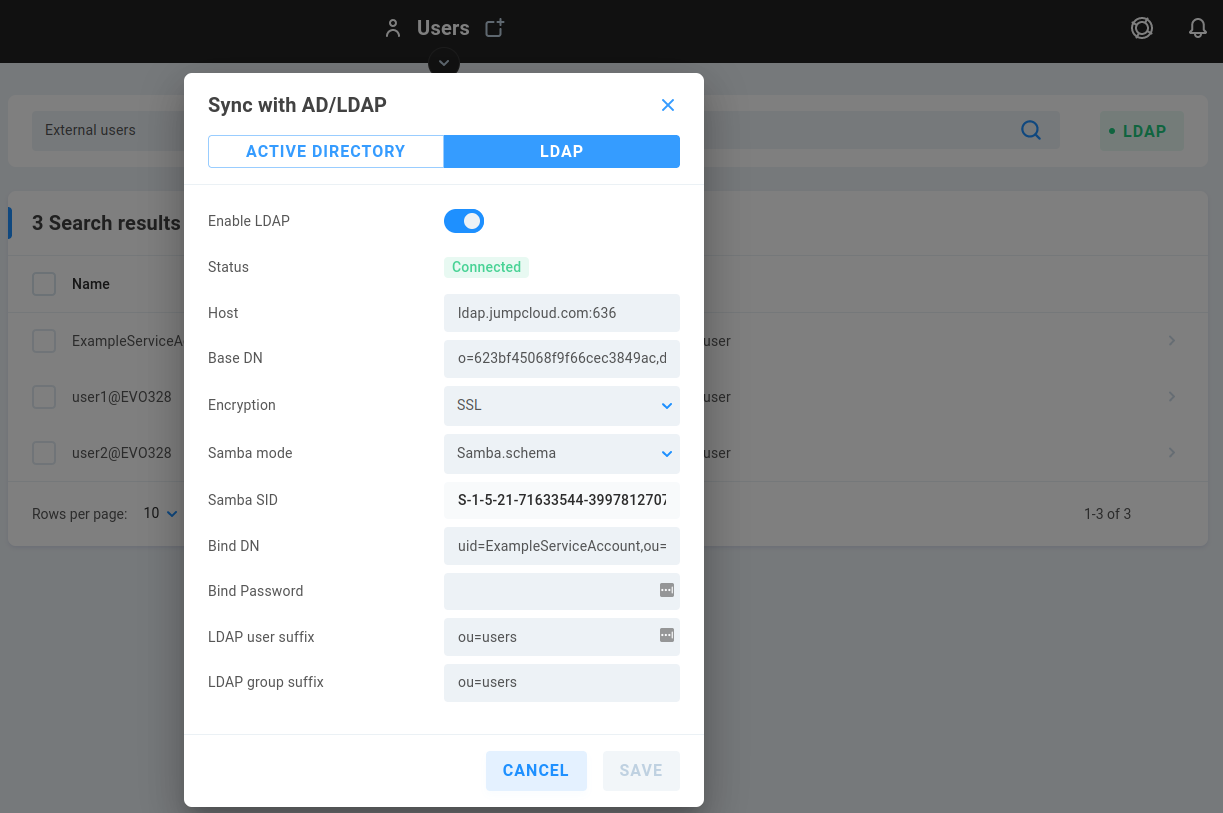
In EVO's web interface at Users > External Users > AD/LDAP, enter:
Host: ldap.jumpcloud.com:636
Base DN: Paste the content copied from the JumpCloud LDAP Details > LDAP Instance > ORG DN field
Encryption: SSL
Samba mode: Samba.schema
Bind DN: Paste the content copied from the JumpCloud LDAP Details > LDAP Configuration > Samba Service Account DN field
Bind Password: Enter the password for the JumpCloud LDAP Binding User account
LDAP user suffix: ou=users
LDAP group suffix: ou=users
Click Save and allow a few moments for authentication.
Be sure to assign SMB permission to users, after which they can mount network shares using their LDAP account.
